No keys are required
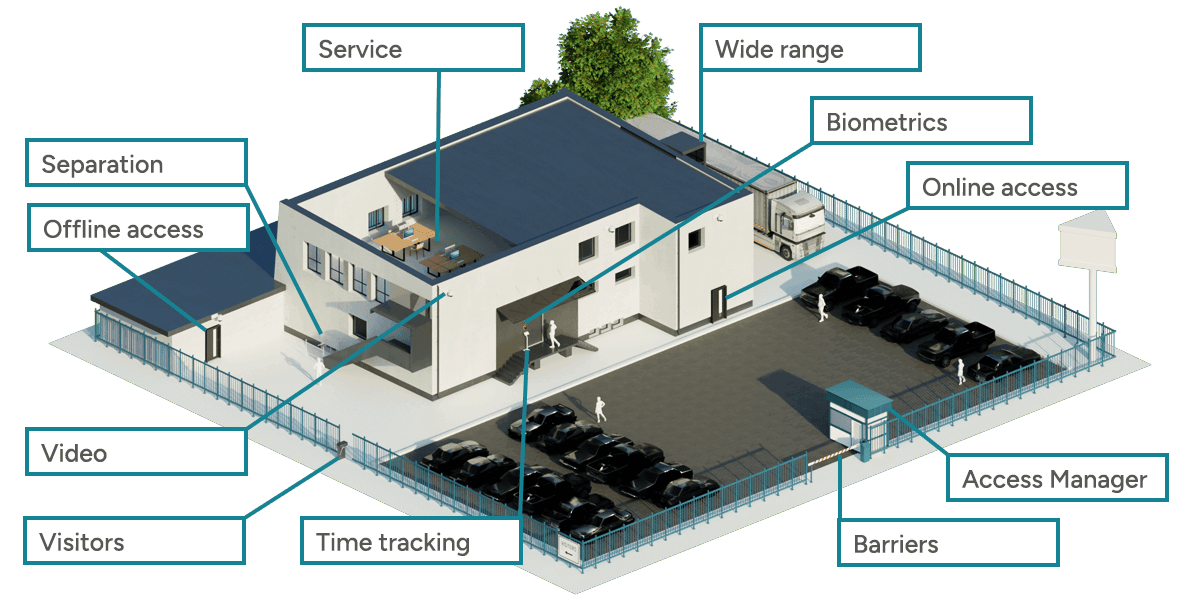
GFOS access control software enables doors and barriers to be controlled with group or individual authorizations, which can also be combined. In this way, employees, visitors and suppliers can open or enter approved areas independently of each other - particularly easily with group-specific IDs that can be printed directly in the GFOS software. In addition, the GFOS access control system makes it easy to define the periods during which the authorizations are active.
Numerous interfaces to other systems, such as SAP's HCM system and the connection to Personio's digital personnel file, ensure smooth digital communication of the access control system. Our services also include compatibility with different hardware manufacturers. Our hardware partners Datafox, dormakaba, GANTNER and PCS Systemtechnik can be perfectly combined with GFOS and adapted to your desired security requirements.
Combine MIFARE or LEGIC readers with biometrics (palm vein pattern authentication or fingerprint) and/or a personal PIN and decide which reading method or biometric process should be used depending on the door or gate. For example, we combine high-security areas with a second factor (biometrics or PIN in combination with RFID). In this way, access is only possible with a combination of the two factors RFID and "Knowing" (PIN) or "Being" (biometrics). All this, as well as suitability for international companies thanks to integrated multilingualism and various evaluation options (GDPR/data protection) make GFOS.Access Control a precisely configurable 360-degree solution for your company.

View all references




The advantages of our access control system
Central administration
GFOS access control simplifies the management of authorizations for you.
Increased security
No more key lists: the access control system manages access for you digitally.
Flexibly expandable
Use the system stand-alone or in combination with visitor management, time tracking software and many other functions.
Hardware mix
Are you already using hardware? You can also combine providers with the GFOS access control software.
Modular expandability
Flexibly expand your software: use the GFOS ecosystem to map your MES, workforce management and access requirements.
Also in the cloud
GFOS solutions are all available in the cloud - so you can remain flexible when it comes to implementation and scaling.
Discover our new packages now
Maximum security with minimal effort – discover our flexible access control bundle.
To the bundle Access ControlControl different locking systems
The GFOS solution maps all of your company's online and offline access in a single access system. For example, IDs for offline access can be updated on demand at online terminals so that even short access durations can be recorded. This keeps your company protected in the event of loss of the means of identification.
Offline door terminals and battery-operated mechatronic cylinders can also become part of the software-controlled access control. Are various access readers and/or electronic locks already being used in your company? Even then, a connection to GFOS.Access Control may still be feasible!
- Integration of various locking systems - battery-operated, wired, with or without radio
- Seamless integration of the offline world into the online one
- Access with smartphone also possible (ID.mobile) - smartphones as a means of identification
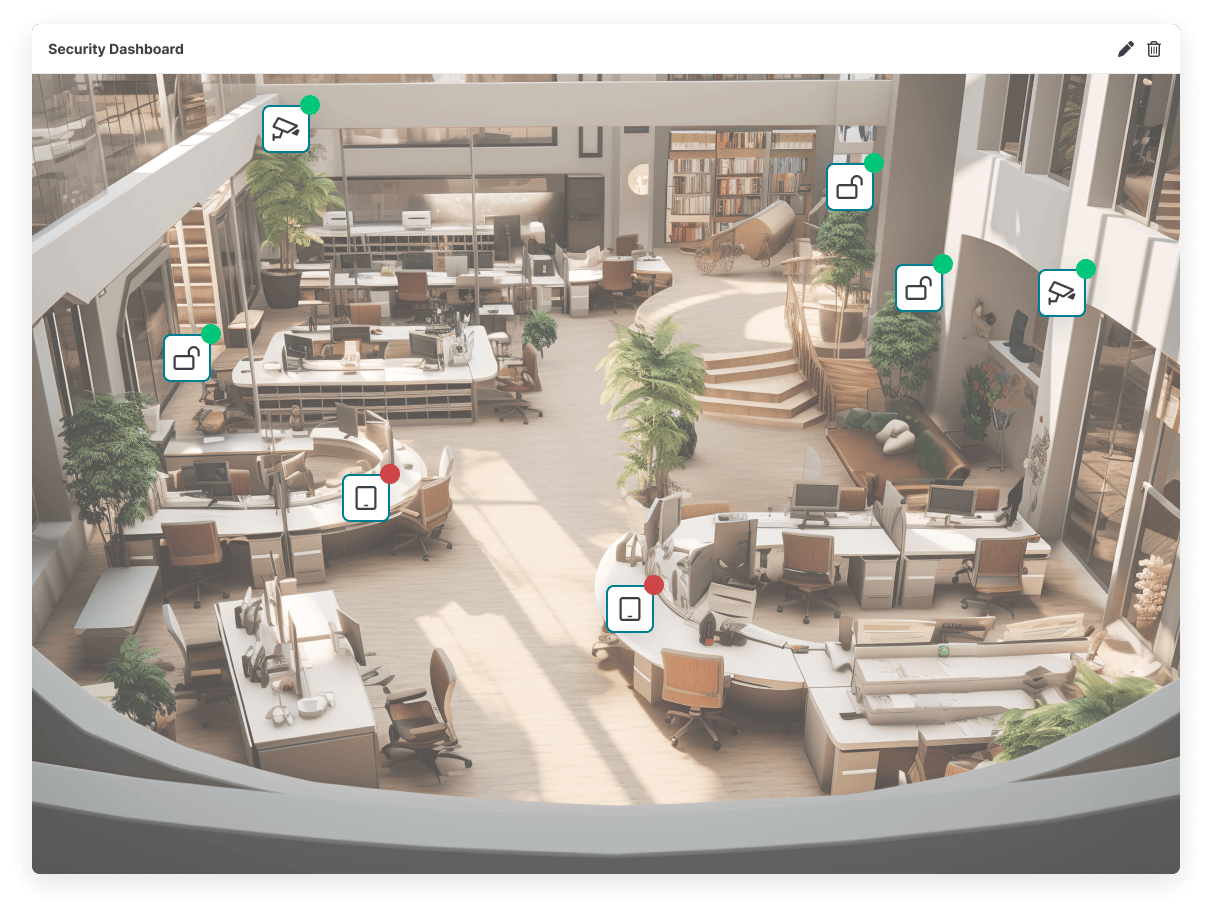
Security dashboard for access control
GFOS offers your company a holistic security concept, the components of which can be mapped in an intuitive dashboard. For example, security officers can quickly view transmissions after integrating video cameras. Integrated alarm management allows all messages from the terminal - including people entering and leaving areas - to be visualized
- Flexible visualization with the help of optionally displayable widgets
- Opening of barriers/doors via softkeys using floor plans
- Can be used by gatekeepers to match people
Access control from GFOS at a glance
Role and authorization concept
Assign individual roles and authorizations in the software for targeted access control system.
Hardware for your requirements
GFOS cooperates with the most popular hardware providers in the German-speaking world. You can connect one to an infinite number of terminals to cover your security requirements.
Clear monitoring
Maintain an overview at all times with the comprehensive security dashboard. You can customize it according to your needs.
Many interfaces
Use the many interfaces from GFOS and seamlessly integrate the access control software into existing IT infrastructures for time tracking software, ERP and more.
Easy ID management
Generate and encode ID cards directly in the software. This allows you to authorize new employees directly for access control system.
Modular structure
Use the modular structure of GFOS solutions to digitally map your MES, workforce management or access requirements.
The access control software successfully in use
Successes with access control software from GFOS

Arthrex GmbH

AVA Abfallverwertung Augsburg

Josef Bernbacher & Sohn GmbH & Co. KG

IMS Gear SE & Co. KGaA

Karl Finke GmbH

MANN+HUMMEL International GmbH & Co. KG

NOWEDA Apothekergenossenschaft eG

Sennheiser electronic GmbH

Transgourmet Deutschland GmbH & Co. OHG

Vollert Anlagenbau GmbH
An access control software makes sense for companies - regardless of the sector in which you work. The size of your company doesn't matter either. You can increase security in your organization many times over by controlling authorizations in a targeted manner and using individual access concepts.
Yes, you can set up different role and authorization concepts, store authorizations and thus precisely control access. You decide who has access to which room or area and when. This allows you to define exactly which of your rooms or areas may be used or entered by whom. The time, person, room and zone can be stored individually in the software.
Our software solution has a general configuration standard that works for many companies. Information on the compatibility of the GFOS software can be found in our system requirements. These are standard requirements. If you have further or more individual requirements, we will find a solution together. Our IT experts will be happy to advise you on your project.
The GFOS software works independently of hardware. This means that you can of course continue to use the hardware you are already using. We work together with the four market-leading software-independent hardware providers from the DACH region and can therefore develop tailor-made hardware solutions for you. Further information can be found in the information on our security partner companies.
Your access control system will continue to function completely autonomously. If you also use a UPS system (uninterruptible power supply), you are also protected against a power failure.
The transponder and therefore the authorizations can be blocked in the software. This means that this transponder will no longer be granted access once it has been blocked and your company will continue to be protected.
Yes, the GFOS software world has a modular structure. This means you can use the entire GFOS ecosystem according to your requirements and integrate solutions for your production control or time tracking software, for example. Connection to your existing IT system landscape is also effortless, for example through our interfaces to SAP. Take a look at our interfaces and partner companies.
Yes, you can also use all GFOS software in the GFOS knownCloud. This allows you to implement the solutions much faster and scale them at any time if required. Our IT experts take care of updates and much more.
Why GFOS software is worthwhile
Users: 7 million
On average, 7 million users utilize GFOS software every day. This is how we digitize working environments worldwide and ensure future success - from SMEs to international corporations.
Custom Interfaces 70+
The system is perfectly integrated into your existing IT system landscape with over 30 interfaces to payroll accounting systems and over 40 interfaces to ERP systems.
Countries: 30
Our software is serving to cut labor costs substantially in over 30 countries.
Languages: 18
GFOS solutions are available in 18 languages. This means you benefit from the international deployment options.
Experience: 35+ years
With over 35 years of success and a broad partner network, we offer cross-industry solutions for companies of all sizes.
Want to get the GFOS access control software for your company or want more information about it? Then just get in touch with us!:
Tatjana Buchholz
+49 (0)201 / 61 30 00
buchholz.tatjana@gfos.com
Contact

