What Is KRITIS?
“KRITIS” is a German acronym for critical infrastructure. It refers to sectors where temporary or prolonged disruptions can cause severe operational impact and, in the worst case, put people at risk.
In Germany, this includes industries such as manufacturing, logistics and transportation, food production, and healthcare. Many of these are “blue-collar” environments where on-site operations are central and physical access needs to be managed as carefully as digital access.
Germany’s Federal Office for Information Security (BSI) lists additional sectors (including IT and public administration) on its overview page. For these sectors and the organizations that operate within them, elevated requirements for (digital) security are a necessity.
What Is the NIS2 Directive?
The NIS2 Directive (Directive (EU) 2022/2555) is an EU-wide framework designed to strengthen cybersecurity across Europe. It replaces the original NIS1 Directive (2016/1148). In Germany, its requirements became legally effective on 12/06/2025 through the “NIS2 Implementation Act.”
One of the most significant changes is the directive’s much broader scope of application. In short: NIS2 applies to far more sectors than its predecessor.
Key changes introduced by NIS2 include:
- A mandatory national cybersecurity strategy (national level)
- Implementation of cybersecurity risk management measures
- Expanded applicability across 18 sectors
- Classification of “essential” and “important” entities
- Mandatory registration with the BSI for affected entities
- Stricter incident reporting obligations
- Personal liability for executive management and responsible leaders
What this means for companies: NIS2 clearly applies to KRITIS entities. At the same time, organizations outside the classic critical infrastructure definition can still fall under NIS2 depending on sector, size, and business relevance.
To help organizations assess their situation, the BSI provides a NIS2 applicability check. Using the online questionnaire, companies can review whether they will (likely) be required to comply. Key factors include the sector, company size, annual revenue, and more.
What NIS2 Requires: Practical Obligations for KRITIS and Other Organizations
In this section, we summarize the new and expanded obligations that KRITIS operators and other in-scope organizations need to implement.
Risk-Based Information Security Management
Organizations need to implement an internal Information Security Management System (ISMS) that helps them identify operational risks and define appropriate controls based on risk level.
Building a comprehensive risk landscape takes time at the start. However, a well-defined security policy ensures there are clear responses for realistic scenarios, with documented decision paths and ownership so teams can act quickly under pressure.
Incident Reporting and Initial Notification
If a security incident materially impacts either the service itself and/or its users, organizations must follow several reporting steps within defined timelines.
An initial notification must be submitted within 24 hours of becoming aware of the incident. A more detailed incident report must follow within 72 hours. No later than one month after the incident, a comprehensive final report must be uploaded via the BSI reporting portal.
Business Continuity and Emergency Planning
NIS2 requires KRITIS operators to develop actionable emergency and continuity plans early on, closely aligned with the ISMS. This includes business continuity strategies and recovery plans so outages and disruptions cause as little damage as possible.
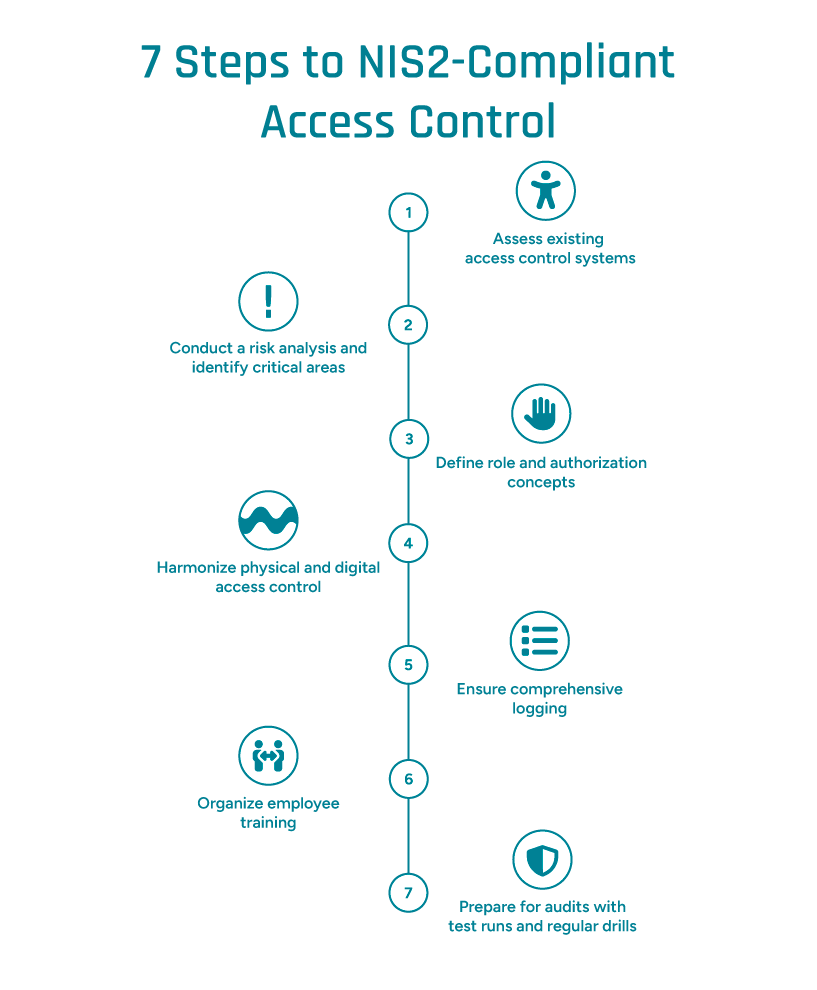
Access Control and Personnel Security
Under NIS2, physical access control moves even more into focus. Article 21 explicitly requires organizations to protect physical entry to business-critical areas with the same rigor as digital access to systems. Controls may include role-based access rights and Zero Trust principles.
In practice, this means tighter control and logging for entry to sensitive areas, for example via smart access readers. It also means treating physical access as a core part of the digital security strategy and incorporating site-specific scenarios into risk assessments.
Comprehensive Documentation and Evidence Requirements
All security-relevant information, from the authorization concept to evacuation procedures, must be clearly documented and easy to access, both for internal stakeholders during an incident and for authorities such as the BSI to verify NIS2 compliance.
Among other requirements, organizations must be able to provide evidence of which controls apply to which parts of the business and which employees have access to highly sensitive areas or data. KRITIS operators should expect their documentation to be reviewed as part of audits.
Risks of Noncompliance
NIS2 does not just tighten requirements. For KRITIS-adjacent organizations, failure to meet the obligations can result in significant penalties. Executive leaders may also face personal liability for ensuring the required security measures are implemented correctly.
Under NIS2, fines scale based on an organization’s classification:
- Essential entities: up to €10 million or 2% of global annual revenue
- Important entities: up to €7 million or 1.4% of global annual revenue
Beyond financial impact, organizations also face potential reputational damage and prolonged operational disruption. In other words: while implementation requires effort, the cost of partial, incorrect, or missing NIS2 compliance can be far more severe for KRITIS-adjacent organizations.
Under the NIS2 directive, physical access to KRITIS facilities must be secured with the same rigor as digital access rights; © GFOS Group
How NIS2 Impacts HR Leaders
Cybersecurity goes far beyond the workstation. Every employee with access to KRITIS-adjacent sites can be both a risk factor and a key part of your security posture. HR leaders need to account for this dual role and reflect it in workforce planning, onboarding, and training.
Shift Work and Production Floors as Potential Entry Points
In shift operations, people enter and leave the site continuously. Who ensures no unauthorized person slips in? Not every plant has an anti-passback mechanism in place to prevent badge sharing or tailgating.
Going forward, organizations need to treat these access-control details as a core part of their security strategy from day one, including ongoing employee training and clear operational rules.
Balancing Access Rights and Data Privacy
KRITIS-adjacent organizations need visibility into who is on-site and when, and who is not. Features such as a digital evacuation list can serve a critical dual purpose. At the same time, leaders must ensure that employee data usage, for example for presence tracking or on-site time recording, remains strictly compliant with GDPR requirements.
Connecting Access Control With HR Systems
One of the simplest and most reliable ways to manage authorizations and access control is to integrate an access-control solution with your HR system. This keeps employee-related data centralized and protected, supports data integrity, and can also simplify external audits.
NIS2 and KRITIS: Access Control Under the Directive
Access Control is an even more central building block under NIS2 than it was under the previous directive. In KRITIS-adjacent organizations, it ideally brings together digital access, physical entry, and authorization data in a single, consistent layer.
From there, organizations must ensure that sensitive areas and systems are accessible only to authorized individuals, and that approvals are managed in a traceable way. This is not a one-time project, but a continuous process.
In practice, this means reviewing access zones and permission structures, removing excessive privileges, modernizing access credentials (such as encrypted employee badges), and continuously documenting every change.
At GFOS, we support customers end to end: from expert consulting to modern access systems and current locking standards (LEGIC advant) through to NIS2-aligned documentation. We help KRITIS-adjacent organizations implement access control in a way that stands up to operational realities and audit requirements.
Use Cases: Integrated Access Control in Practice
Linking workforce data with your security infrastructure delivers clear benefits in day-to-day operations for HR and IT alike. The following industry examples illustrate why:
- Manufacturing: In production, it is essential that only qualified employees operate specific machines. A digital workforce planning solution combined with skill management software helps ensure that each shift is staffed only with employees who have the required qualifications. When connected to access control, only the employees scheduled for that shift receive entry to the site.
- Logistics: In logistics operations, entry permissions, fleet access, and sensitive zones should be tied to specific roles and verified credentials. Driver qualifications (for example, commercial licenses), approvals, and roles can be matched digitally with workforce data and enforced via access control.
These simple examples highlight an important point: once workforce planning and qualification management streamline scheduling, connecting an access control solution is often a small, complementary step.
At the same time, especially with a flexible system like GFOS, this step can materially strengthen NIS2 compliance for KRITIS-adjacent organizations by aligning people, permissions, and audit-ready documentation.
Implement NIS2 Requirements With GFOS
Access control is a foundational element of a secure site. We would be happy to advise you on your options with GFOS. Explore our bundle for access management tailored to your requirements.